

There are a surprising number of grammatical errors in that blog post. Did anyone proof read it, I wonder?
All of this user’s content is licensed under CC BY 4.0.


There are a surprising number of grammatical errors in that blog post. Did anyone proof read it, I wonder?


For sure. What the aforementioned bits of information provide is the ability to be confident in the privacy of software if one were to treat it as a black box, ie an average consumer.


Hm, I feel that it’s inaccurate to say “we wouldn’t be able to tell”. It’s not exactly a black box system — the app would have to run on an operating system, and if you are able to know what the operating system is doing, and what instructions are being executed by the CPU, then you can know exactly what the app is doing.
What the aforementioned bits of information provide is the ability to treat software as a black box and be sure of its safety without having to fundamentally audit it.
Windows -> Ubuntu -> Arch Linux


Without it being open source and not providing reproducible builds, the privacy claims are borderline weightless.


Nearly 90% of their servers are blocked to do common internet tasks .
Perhaps your browsing habits are severely impacted by Mullvad being blocked, but that doesn’t seem to be the universal case. I’ve had the occasional hiccup with a few sites that block VPNs (Mullvad’s IPs), but “90%” is quite an exaggeration when compared to my personal experience.


But it’s icky so many people still think it should be illegal.
Imo, not the best framework for creating laws. Essentially, it’s an appeal to emotion.


It’s a nigligible inconvenience
This community is called Mildly Infruating, after all 😜


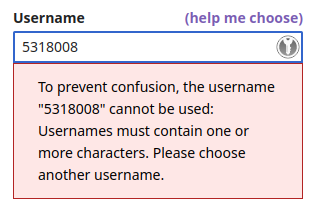
Ha, that username is apparently not allowed. They require that a username contain at least one letter.


Just the environment where the impersonations are theorized to take place — given the type of people who likely use the service, the ways people interract on the site, what the site is used for… imo, it seems unlikely that changing an “a” to a “4” is going to result in a damaging impersonation.


That certainly does seem to be their goal, but, imo, it’s a bit extreme — especially given the context.


doas, afaik, was originally made for FreeBSD, so some of its features aren’t compatible with/haven’t been implemented for Linux. That may or may not be an important issue for you to consider.


It depends on how interested/motivated you are in finding out exactly why things aren’t working. If you just want a working system without the hassle, since it’s a fresh install, I’d recommend just reinstalling.
How do you compare it with Pacman?
Apt is the greatest package manager ever built.
What’s your rationale for making that claim?
If for example my Firefox were to be compromised and started not only talking to Firefox Sync to send the history to my phone, but also send my behavior and all the passwords I type in to a third party… How would the firewall know?
If it’s going to some undesirable domain, or IP, then you can block the request for that application. The exact capabilities of the application layer firewall certainly depend on the exact application layer firewall in question, but this is, at least, possible with OpenSnitch.
It’s just random outgoing encrypted traffic from its perspective.
For the actual content of the traffic, is this not the case with essentially all firewalls? They can’t see the content of te traffic if it is using TLS. You would need to somehow intercept the packet before it is encrypted on the device. I’m not aware of any firewall that has such a capability.
If you just click on ‘Allow’ there is no added benefit.
The exact level of fine-grain control heavily depends on the application layer firewall in question.
A maliciously crafted request or answer to your software can trigger it to fail and do something that it shouldn’t do.
Interesting.
I think now it’s just the first, plus they can ask for a fixed amount of money since by your negliect, you caused their lawyer to put in some effort.
I do, perhaps, somewhat understand this argument, but it still feels quite ridiculous to me.
But this is a really difficult thing to protect from. If someone gets to push code on my computer that gets executed, I’m entirely out of luck. It could […] send data […].
Not necessarily. An application layer firewall, for example, could certainly get in the way of it trying to send data externally.
On the other hand it could happen not deliberately but just be vulnerable software.
Are you referring to a service leaving a port open that can be connected to from the network?
And then also run Lemmy, Matrix chat and a microblogging platform on it.
I’m definitely curious about the outcome of this – Matrix especially. Perhaps the new/alternative servers function a bit better now, but I’ve heard that, for synapse at least, Matrix can be very demanding on hardware to run (from what I’ve heard, the issues mostly arise when one joins a larger server).
You’re considered a “disruptor” and can be held responsible, especially to stop that “disruption”.
Interesting. Do you mean “held responsible” to simply stop the disruption, or “held responsible” for the actions of/damaged caused by the disruption?
for example detect which network was connected to and re-configure the packet filter.
Firewalld is capable of this – it can switch zones depending on the current connection.
And while I think that is not a good argument at all, I feel protected enough by using the free software I do and roughly knowing how to use a computer. I don’t see a need to install a firewall just to feel better. Maybe that changes once my laptop is cluttered and I lose track of what software opens new ports.
There does still exist the risk of a vulnerability being pushed to whatever software that you use – this vulnerability would be essentially out of your control. This vulnerability could be used as a potential attack vector if all ports are available.
I’m currently learning about Web Application Firewalls. Maybe I’ll put ModSecurity in-front of my Nextcloud.
Interesting! I haven’t heard of this. Side note, out of curiosity, how did you go about installing your Nextcloud instance? Manual install? AIO? Snap?
I’m personally not a friend of that kind of legislation. If somebody uses my tools to commit a crime, I don’t think I should be held responsible for that.
It would be a rather difficult thing to prove – one could certainly just make the argument that you did, in that someone else that was on the guest network did something illegal. I would argue that it is most likely difficult to prove otherwise.
Enable access when you’re at your workplace but inhibit the Windows network share when you’re at the airport wifi.
How would something like this be normally accomplished? I know that Firewalld has the ability to select a zone based on the connection, but, if I understand correctly, I think this is decided by the Firewalld daemon, rather than the packet filtering firewall itself (e.g. nftables). I don’t think an application layer firewall would be able to differentiate networks, so I don’t think something like OpenSnitch would be able to control this, for example.
But an approach like this isn’t perfect by any means. The IoT devices can still mess with each other. Everything is a hassle to set up. And the WiFi is a single point of failure.
What would be a better alternative that you would suggest?
You can also set up a VPN that connects specifically you to your home-network or services. Your Nextcloud server can’t be reached or hacked from the internet, unless you also have the VPN credentials to connect to it in the first place.
The unfortunate thing about this – and I have encountered this personally – is that some networks may block VPN related traffic. You can take measures to attempt to obfuscate the VPN traffic from the network, but it is still a potential headache that could lock you out of using your service.
Ah, right. I forgot that they’re based in Sweden. That’s understandable if it’s simply a lack of familiarity with the language, but, still, I would expect a company like Mullvad to at least have one native-equivalent English speaker to look over their public facing English stuff. None of this is the end of the world, ofc — I’m just mildly surprised.